Researchers at the Complexity Science Hub (CSH) devise a straightforward yet effective method to assist law enforcement in efficiently managing the influx of data in cybercrime.
Crimes related to cryptocurrencies are overwhelming law enforcement agencies. However, the challenge lies in navigating the vast amounts of data. Identifying connections between cases is crucial to prevent multiple agencies from working on the same incidents, says CSH researcher Bernhard Haslhofer. In collaboration with the Bavarian Central Office for the Prosecution of Cybercrime (ZCB), he has developed a simple yet effective solution.
To identify connections between cybercrime cases, the research team follows the trail of money. Cryptocurrencies have emerged as a global means of payment and are utilized in a variety of crimes such as “sextortion” or “cybertrading fraud.”
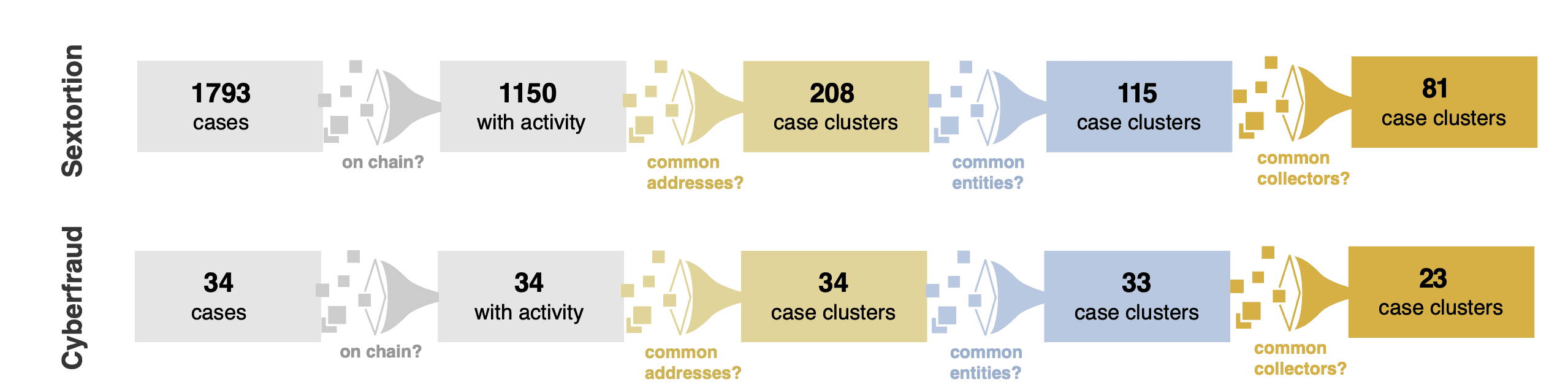
- The team has investigated 1,793 cases of sextortion and 34 cases of cybertrading fraud.
- While 41% of cybertrading fraud cases are connected, in sextortion cases, it’s almost 97%.
- Researchers followed the money trail, typically involving crypto assets such as Bitcoin.
97% OF SEXTORTION CASES ARE CONNECTED
“In our study of 1,793 sextortion cases, we found that 96.9% are interconnected,” explains Bernhard Haslhofer, Head of the Cryptofinance research group at CSH. Sextortion involves online scams where victims are blackmailed by strangers pretending to release compromising photos or videos.
Similarly, 41% of the 34 examined cases of cybertrading fraud showed connections. All these cases were reported to the ZCB between January 2021 and July 2023. Early recognition of such case connections is key to managing the rapidly rising numbers in cybercrime, according to Haslhofer.
A GLOBAL CHALLENGE
Typically, individuals who fall victim to internet crime file reports with their local police station. If the police lack the means to recognize connections between cases and instead investigate individual crimes in isolation, multiple agencies may end up working on the same cases. Cybercriminals almost always operate across regions, managing numerous platforms with different domains and in various countries.
FOLLOWING THE MONEY TRAIL
To facilitate future identification of case connections and information exchange among investigators, the research group developed a simple yet effective tool. This tool follows the money trail, primarily involving crypto assets like Bitcoin. In the simplest scenario, different victims pay into the same crypto address, establishing a connection. Additionally, researchers have clustered all crypto addresses, for example, based on similar input addresses. “Locating multiple cases in one cluster indicates a connection between these cases,” explains Haslhofer. The same applies to payment streams from different clusters leading to an identical target account.
BILLIONS IN OVERALL DAMAGES
“For example, at the Bavarian Central Office for the Prosecution of Cybercrime (ZCB), five prosecutors are currently investigating more than 1,600 fraudulent cybertrading platforms that caused a total damage of around 250 million euros. Thousands of cases from individual victims are landing on our desks,” explains Chief Prosecutor Thomas Goger of the ZCB, outlining the magnitude of the challenge. The overall damage in Germany alone is likely to reach into the billions.
“More personnel and licenses for expensive forensic tools alone will not be sufficient to keep pace with the rapidly increasing case numbers. Therefore, we must comprehensively address the problem structurally and identify networks,” says Haslhofer. This approach can significantly enhance the efficiency of investigations, especially when case connections can be extended across crime areas, international borders, and jurisdictions.
THE BAVARIAN CENTRAL OFFICE FOR THE PROSECUTION OF CYBERCRIME (ZCB)
Since January 1, 2015, ZCB has been in operation at the Public Prosecutor’s Office in Bamberg, Germany. This central office is responsible statewide for handling prominent investigative proceedings in the field of cybercrime. The cases it deals with are diverse, ranging from hacking attacks and cases of online advance payment fraud, such as those involving professional fake shops, to incidents of ransomware and illicit trade in weapons, drugs, and counterfeit money on the darknet. Additionally, the ZCB is responsible for prominent cases of economic cybercrime.
Since October 1, 2020, the ZCB has also housed the Center for Combating Child Pornography and Sexual Abuse on the Internet. This specialized unit focuses particularly on operators and users of darknet forums involved in the production, posting, or trafficking of child pornography.
Currently, the ZCB employs 24 prosecutors and four IT forensic experts.
About the study
The authors recently presented the results of the study, “Increasing the Efficiency of Cryptoasset Investigations by Connecting the Cases,” at the APWG Symposium on Electronic Crime Research. The paper is available for download on the preprint server arXiv.